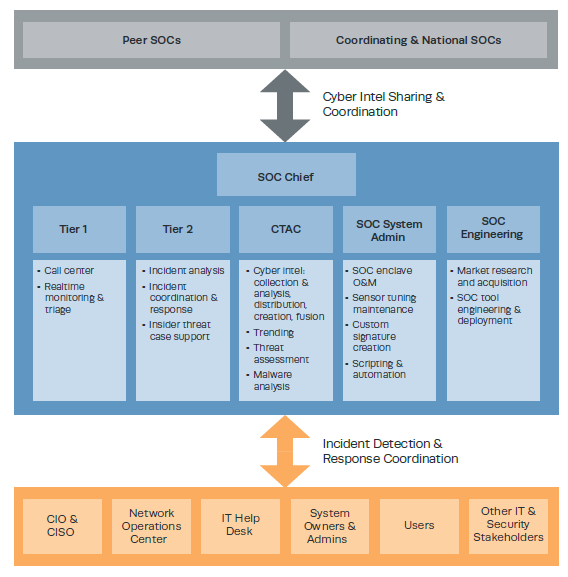
A key component of a SOC is the cyber threat analysis cell (CTAC). The following figure from the Zimmerman manual illustrates how a CTAC functions within the SOC (2014).
With the 2021 issuance of STIX 2.1 and TAXII 2.1 the protocol suite for sharing of machine readable threat intelligence will have crossed a key milestone. Government agencies, not-for-profit organizations, companies, ISACs and ISAOs will all have a common language and data model that will reduce uncertainty about what is being shared, and how to share it. To really benefit from this sharing regime both producers of threat data feeds and consumers of threat data must get to know the STIX data model and how it can be used to characterize the larger threat landscape. CTACs, in particular, must be familiar with STIX and knowledgeable about using it to their best advantage.
______________________________________
Reference:
Zimmerman, C. (2014). Ten Strategies of a World-Class Cybersecurity Operations Center. The Mitre Corporation.